Cybersecurity? - “Do I feel lucky?”
Follow articleHow do you feel about this article? Help us to provide better content for you.
Thank you! Your feedback has been received.
There was a problem submitting your feedback, please try again later.
What do you think of this article?
That’s’ a quote from one of my all time favourite movies. Here’s the full quote for Harry fans:
“I know what you're thinking. "Did he fire six shots or only five?" Well to tell you the truth in all this excitement I kinda lost track myself. But being this is a .44 Magnum, the most powerful handgun in the world and would blow your head clean off, you've gotta ask yourself one question: "Do I feel lucky?" Well, do ya, punk?
What’s this got to do with Cybersecurity?
You've got to ask yourself one question. “Do I feel lucky about the security of my automation control system, and its robustness to a cyber attack?” If you are reading this article when published [2017], then the chances are that you have not been impacted by a cybersecurity breach …yet. However, statistics indicate it’s only a matter of time with a +2100% increase in the number of cybersecurity incidents over last 3 years rising to 140 million incidents in 2015, and an estimated 300,000 new malware programs now being created daily…
Is this relevant to my Automation Control System?
We can understand why Industrial Control and Automation systems are now under threat – Go back a decade or two, and generally, control systems were not connected to the outside world. They would have generally used proprietary software and communication protocols, making them nigh on impossible to connect to in an unauthorized manner. Control systems have evolved with IIoT technology, smart devices with open Ethernet communications, on-board webservers providing easy to navigate system and application diagnostics. Control systems are connected. This could be to the outside internet, but more likely to intranets, or to allow for remote connection for monitoring and diagnostics.
Where do the threats come from ?
News stories about cybersecurity attacks are all too frequent. Malicious terrorist attacks that target large manufacturers or critical infrastructure. Others where invisible hackers are phishing or searching for soft undefended targets. These hostile attacks, or theft of intellectual property or private information may seem less relevant to the average small/medium sized user of automation equipment. However threats can come in from different sources – and all can have devastating impact on the run-time, performance, efficiency and safety of the application being controlled. Closer to home these threats can come from within the organization, or supply chain. The most vulnerable point is the people who administer the systems – and cyber threats could be intentional (the disgruntled employee) or accidental (where the right levels of defence are not installed).
Not one, but Four Questions
Anyone signing the cheque for new investment in cybersecurity solutions will first need an understanding of the level of risk and implications before possible solutions can be evaluated. As equally important however is the ongoing maintenance and updating of the cybersecurity system once created. We can expand our first question to four key questions. If an unauthorized user can get access to my control system:
- What could go wrong ?
- What is the impact (personnel / environment, safety, lost production, financial recovery) ?
- What do we have in place (or need in place) to prevent this from happening ?
- How do we ensure that (3) is working ?
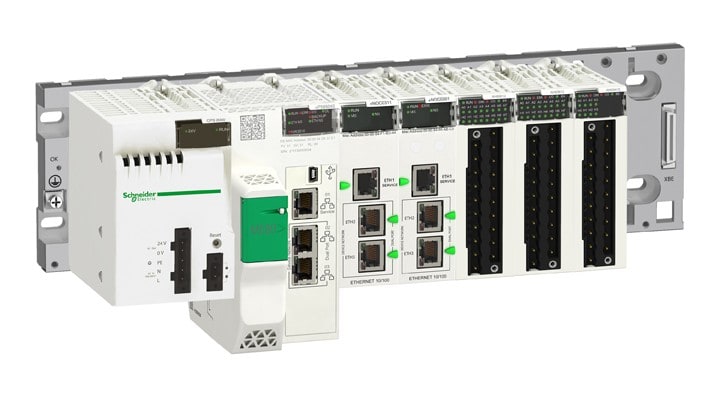
Cybersecurity certification - Achilles Level 2

Modicon M580 ePAC Controller - Achilles Level 2 certified
Defence in Depth
- Security planning
- Network separation
- Perimeter protection
- Network segmentation
- Device hardening
- Ongoing system monitoring and updating